17.CAFFE LATTE ATTACK:
In the Honeypot attacks , we notice that clients will continuously probe for SSIDs they have
connected to previously. If the client had connected to an access point using WEP, operati ng
systems such as Windows, cache and store the WEP key. The next ti me the client connects to
the same access point, the Windows wireless confi gurati on manager automati cally uses the
stored key.
The Caffe Latte attack is a WEP att ack which allows a hacker
to retrieve the WEP key of the authorized network, using just the client. The attack does not
require the client to be anywhere close to the authorized WEP network. It can crack the WEP
key using just the isolated client.
In this exercise, we will retreive the WEP key of a network from a client using the Caffe
Latte attack.
CONDUCTING THE CAFFE LATTE ATTACK:
Follow these instructi ons to get started:
STEP 1:
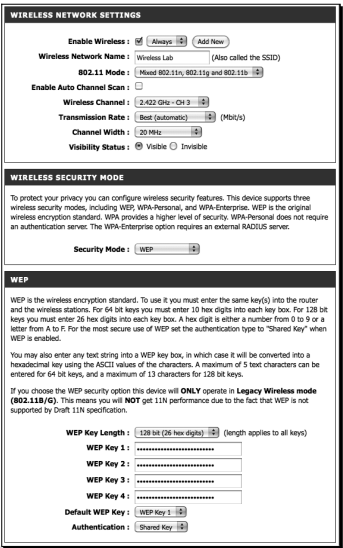
Let us fi rst set up our legiti mate access point with WEP for the network Wireless Lab
with the key ABCDEFABCDEFABCDEF12 in Hex:
STEP 6:
We now start airodump-ng to collect the data packets from this access point only,
as we did before in the WEP-cracking case:
STEP 7:
We also start aircrack-ng as in the WEP-cracking to begin
the cracking process. The command line would be aircrack-ng filename where
filename is the name of the file created by airodump-ng :
STEP 8:
Once we have enough WEP encrypted packets, aircrack-ng succeeds in cracking
the key as shown next:
THANKS FOLKS....
In the Honeypot attacks , we notice that clients will continuously probe for SSIDs they have
connected to previously. If the client had connected to an access point using WEP, operati ng
systems such as Windows, cache and store the WEP key. The next ti me the client connects to
the same access point, the Windows wireless confi gurati on manager automati cally uses the
stored key.
The Caffe Latte attack is a WEP att ack which allows a hacker
to retrieve the WEP key of the authorized network, using just the client. The attack does not
require the client to be anywhere close to the authorized WEP network. It can crack the WEP
key using just the isolated client.
In this exercise, we will retreive the WEP key of a network from a client using the Caffe
Latte attack.
CONDUCTING THE CAFFE LATTE ATTACK:
Follow these instructi ons to get started:
STEP 1:
Let us fi rst set up our legiti mate access point with WEP for the network Wireless Lab
with the key ABCDEFABCDEFABCDEF12 in Hex:
STEP 2:
Let us connect our client to it and ensure that the connection is successful using airodump-ng as shown next:
STEP 3:
Let us unplug the access point and ensure the client is in the un-associated stage
and searching for the WEP network Wireless Lab:
STEP 4:
Now use airbase-ng to bring up an access point with Wireless Lab as the SSID
with the parameters shown next:
STEP 5:
As soon as the client connects to this access point, airbase-ng starts the CaFFe-
Latte attack as shown:We now start airodump-ng to collect the data packets from this access point only,
as we did before in the WEP-cracking case:
STEP 7:
We also start aircrack-ng as in the WEP-cracking to begin
the cracking process. The command line would be aircrack-ng filename where
filename is the name of the file created by airodump-ng :
STEP 8:
Once we have enough WEP encrypted packets, aircrack-ng succeeds in cracking
the key as shown next:
THANKS FOLKS....










Good post you should try have a look at my website that is:
ReplyDeleteEthical Hacking Articles®
You may find it in your best and informative.
Thanks Rehan..Just Now Got Up With Your Blog...You Hav Got Too Good posts There..
ReplyDelete